Part 5 in a series
This part is the final post of the series; it builds on the previous posts by adding an SSL-based content switch on top of our previously-created simple HTTP content switch.
The NetScaler does a fine job of handling SSL traffic in a manner similar to the way it handles the unencrypted HTTP traffic. The key differentiator—other than making sure to distinguish the traffic as being SSL-bound—is the inclusion of certificate handling.
Of course, the "outside" or Content Switching virtual server must have an SSL certificate; the client trying to reach your host(s) is expecting an SSL connection, so the listener responding to the particular host request must respond with a conforming certificate or he/she will have to deal with certificate errors.
The "inside" server that's the target of Content Switching probably wants to communicate with its clients using SSL, too (In some special cases—known as "SSL Offload"—the inside server allows non-encrypted connections from specific hosts that are pre-configured to handle the overhead of SSL encryption; NetScaler can do this, too). In order for the NetScaler to perform as a proxy, it must have sets of SSL certificates for both the inside and the outside connections. Once you have those, you can quickly set up an SSL-based content switching configuration that mirrors the HTTP setup.
And the best part? Only the Content Switching virtual server needs to have an SSL certificate that is signed by a trusted root! (Caveat: it must be either a wildcard or multiple-SAN certificate. Remember: the DNS name must match either the CN [common name] or one of the DNS SAN [subject alternate name] entries of the host certificate) The "inside" servers that you're putting "behind" the NetScalers can have self-signed certificates or certificates signed by an in-house CA.
A little about Certificate files
The NetScaler has a ton of flexibility for working with many certificate formats—PEM and DER encoding, PKCS#12 bundles, etc.—but I find that it's easiest and most flexible when using individual, single-certificate (or key) PEM-type, Base64-encoded text files. It's easiest if you just have them ready-to-go; if you don't, you can learn about using OpenSSL, or you can simply use an online converter like SSL Shopper's Certificate Tools. Personally, I use a local copy of OpenSSL.
For the purpose of this tutorial, I'm going to assume you have all the certificates you need, already in PEM format.
SSL handling in the NetScaler
The SSL feature must be enabled to do any sort of SSL load balancing or proxy configuration; it is enabled in the same place that Load Balancing and Content Switching is enabled, off the System->Settings menu:
Preparing Certificates
Once that's enabled, the yellow warning symbol for the Traffic Management function disappears. The first step to managing certificates is to get certificate files uploaded to the NetScaler. Select the SSL option itself:
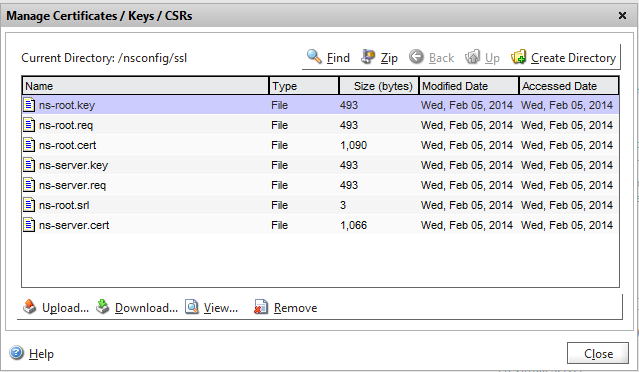
then "Manage Certificates / Keys /CSRs" in the Tools section of the right-hand column.
The dialog resembles a file management window because it essentially is: it's a tool that lets you upload certificate files to the NetScaler's certificate store. Click [Upload...] to load the certificate files on the NetScaler. You'll need both the certificate and its private key, plus any CA certificates—including intermediates—that were used in a signing chain.
Once you have your certificates loaded, close the file dialog and expand the SSL menu tree and select Certificates
Click [Install...]. This process both creates a configuration object that the NetScaler can use to bind certificates to interfaces, and it gives you the opportunity to link certificates together if they form a signing chain. Although you can also use this interface to perform the upload function, I find it works more consistently—especially when handling filenames—to upload in one step, then install.
The server certificate itself needs to be installed using both the certificate and its key file; signing CAs can be loaded with just the certificate file.
Once all the certificates in the chain are loaded, select the server certificate and click the [Action] dropdown, then the "Link..." option.
If you've got a recognized file and the CA that signed the file is already installed, it will be pre-selected in the Link Certificate dialog. Click [OK].
Repeat with any other certificates in the chain, back to the CA root.
Creating the Content Switching Configuration
With minor exceptions, we'll follow the same process for creating a standard HTTP content-switching config. Specific differences will be highlighted using italic typeface.
- If they don't exist already, create your server entries. Because I'm building on the work previously documented, my servers are already present.
- Create SSL-based services for the servers; configure https as a monitor:
- Create SSL-based Load Balancing Virtual Servers
- Set the protocol to SSL
- Disable "Directly Addressable"
- Enable the SSL-based service
- Switch to the SSL Tab
- Highlight the server certificate and click [Add >] to bind the certificate to the server
- Create the new Content Switching policies. We can't use the previous ones—even if they're functionally identical—because we're going to use them on a different CS Virtual Server.
- Create (or modify) an SSL-based Content Switching Virtual Server
- Set the protocol to SSL
- Set the IP address for the virtual server. It can be the same address as the HTTP virtual server.
- Insert policies and set targets to SSL-based targets
- Switch to the SSL Tab
- Highlight the server certificate and click [Add >] to bind the certificate to the server
- Highlight the next CA cert in the signing chain; click the drop-down arrow on the [Add >] button and select [as CA >] to add the signing cert.
- Repeat step 5 for all remaining certificates in the signing chain.
- Click [Create] when complete.
Parts in this series:
- Intro to using a reverse proxy
- Getting NetScaler VPX going in your lab
- Intro to Content Switching in the NetScaler
- Configure a basic content-switching application (HTTP)
- Configure an advanced content-switching application (SSL-SSL proxy) (this post)




















Excelent, many thanks for sharing!!
ReplyDeleteNice post. I learn something new and challenging on blogs I stumble-upon on a daily basis. It's always helpful online grocery app in dubai to read through articles from other writers and practice something from their sites.
ReplyDelete